Get a list of all predefined macros:
- How To Download Gcc On Mac Stack Overflow Download
- How To Download Gcc On Mac
- How To Download Gcc On Mac Stack Overflow Chrome
- How To Download Gcc On Mac Stack Overflow Tank
The following variables can vary by compiler, but generally work:
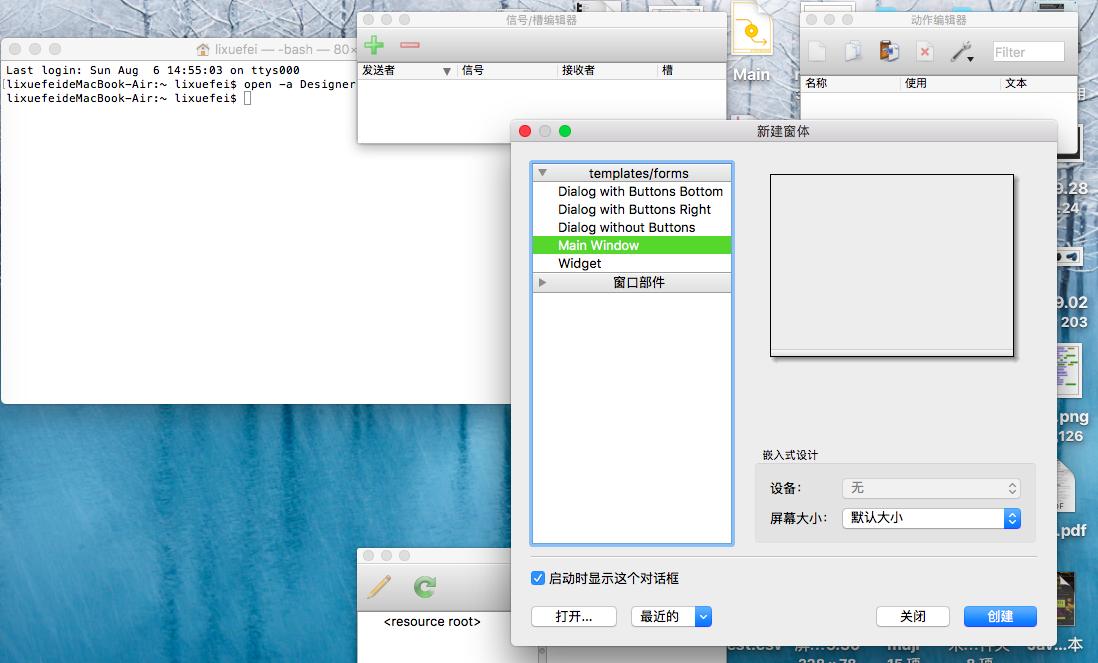
Stack Overflow for Teams is a private, secure spot for you and your coworkers to find and share information. Learn more `conda build gcc-5` Fails on Mac OS Mojave. $ gcc -Wall -fno-stack-protector stacksmash.c -o stacksmash $./stacksmash Enter the name TheGeekStuff len = 26214 len of string entered is: 12 So we see that once the code was compiled with this flag then with the same input, the execution environment was not able to detect buffer overflow that actually happened and corrupted the value of. I'm trying to compile a C application on a Mac. I use SSE4 and AES-NI intrinsics. In Linux, I just call gcc with the -msse4 and -maes flags and include the wmmintrin.h header and I can call SSE. About; Products. Stack Overflow for Teams is a private, secure spot for you and your coworkers to find and share information.
- The __LINE__ and __FILE__ variables represent the current line and current file being processed.
- The __DATE__ variable contains the current date, in the form month/day/year. This is the date that the file was compiled, not necessarily the current date.
- The __TIME__ variable represents the current time, in the form hour:minute:second. This is the time that the file was compiled, not necessarily the current time.
- The __cplusplus variable is only defined when compiling a C++ program. In some older compilers, this is also called c_plusplus.
- The __STDC__ variable is defined when compiling a C program, and may also be defined when compiling C++.
GCC-specific variables
The following are GCC-specific variables. While they are not specifically preprocessor macros they are magic and can be used the same way:
- __func__ contains the bare name of the function
- __FUNCTION__ is another name for __func__
- The __PRETTY_FUNCTION__ contains the type signature of the function as well as its bare name.
Next: Preprocessor Options, Previous: Optimize Options, Up: Invoking GCC [Contents][Index]
3.12 Program Instrumentation Options
GCC supports a number of command-line options that control addingrun-time instrumentation to the code it normally generates. For example, one purpose of instrumentation is collect profilingstatistics for use in finding program hot spots, code coverageanalysis, or profile-guided optimizations.Another class of program instrumentation is adding run-time checking to detect programming errors like invalid pointerdereferences or out-of-bounds array accesses, as well as deliberatelyhostile attacks such as stack smashing or C++ vtable hijacking.There is also a general hook which can be used to implement otherforms of tracing or function-level instrumentation for debug orprogram analysis purposes.
-p-pgGenerate extra code to write profile information suitable for theanalysis program prof (for -p) or gprof(for -pg). You must use this option when compilingthe source files you want data about, and you must also use it whenlinking.
You can use the function attribute no_instrument_function tosuppress profiling of individual functions when compiling with these options.See Common Function Attributes.
-fprofile-arcsAdd code so that program flow arcs are instrumented. Duringexecution the program records how many times each branch and call isexecuted and how many times it is taken or returns. On targets that supportconstructors with priority support, profiling properly handles constructors,destructors and C++ constructors (and destructors) of classes which are usedas a type of a global variable.
When the compiledprogram exits it saves this data to a file calledauxname.gcda for each source file. The data may be used forprofile-directed optimizations (-fbranch-probabilities), or fortest coverage analysis (-ftest-coverage). Each object file’sauxname is generated from the name of the output file, ifexplicitly specified and it is not the final executable, otherwise it isthe basename of the source file. In both cases any suffix is removed(e.g. foo.gcda for input file dir/foo.c, ordir/foo.gcda for output file specified as -o dir/foo.o).See Cross-profiling.
--coverageThis option is used to compile and link code instrumented for coverageanalysis. The option is a synonym for -fprofile-arcs-ftest-coverage (when compiling) and -lgcov (whenlinking). See the documentation for those options for more details.
- Compile the source files with -fprofile-arcs plus optimizationand code generation options. For test coverage analysis, use theadditional -ftest-coverage option. You do not need to profileevery source file in a program.
- Compile the source files additionally with -fprofile-abs-pathto create absolute path names in the .gcno files. This allows
gcovto find the correct sources in projects where compilationsoccur with different working directories. - Link your object files with -lgcov or -fprofile-arcs(the latter implies the former).
- Run the program on a representative workload to generate the arc profileinformation. This may be repeated any number of times. You can runconcurrent instances of your program, and provided that the file systemsupports locking, the data files will be correctly updated. Unlessa strict ISO C dialect option is in effect,
forkcalls aredetected and correctly handled without double counting. - For profile-directed optimizations, compile the source files again withthe same optimization and code generation options plus-fbranch-probabilities (see Options thatControl Optimization).
- For test coverage analysis, use
gcovto produce human readableinformation from the .gcno and .gcda files. Refer to thegcovdocumentation for further information.
With -fprofile-arcs, for each function of your program GCCcreates a program flow graph, then finds a spanning tree for the graph.Only arcs that are not on the spanning tree have to be instrumented: thecompiler adds code to count the number of times that these arcs areexecuted. When an arc is the only exit or only entrance to a block, theinstrumentation code can be added to the block; otherwise, a new basicblock must be created to hold the instrumentation code.
-ftest-coverageProduce a notes file that the gcov code-coverage utility(see gcov—a Test Coverage Program) can use toshow program coverage. Each source file’s note file is calledauxname.gcno. Refer to the -fprofile-arcs optionabove for a description of auxname and instructions on how togenerate test coverage data. Coverage data matches the source filesmore closely if you do not optimize.
-fprofile-abs-pathAutomatically convert relative source file names to absolute path namesin the .gcno files. This allows gcov to find the correctsources in projects where compilations occur with different workingdirectories.
-fprofile-dir=pathSet the directory to search for the profile data files in to path.This option affects only the profile data generated by-fprofile-generate, -ftest-coverage, -fprofile-arcsand used by -fprofile-use and -fbranch-probabilitiesand its related options. Both absolute and relative paths can be used.By default, GCC uses the current directory as path, thus theprofile data file appears in the same directory as the object file.In order to prevent the file name clashing, if the object file name isnot an absolute path, we mangle the absolute path of thesourcename.gcda file and use it as the file name of a.gcda file. See similar option -fprofile-note.
When an executable is run in a massive parallel environment, it is recommendedto save profile to different folders. That can be done with variablesin path that are exported during run-time:
%pprocess ID.
%q{VAR}value of environment variable VAR
-fprofile-generate-fprofile-generate=pathEnable options usually used for instrumenting application to produceprofile useful for later recompilation with profile feedback basedoptimization. You must use -fprofile-generate both whencompiling and when linking your program.
The following options are enabled:-fprofile-arcs, -fprofile-values,-finline-functions, and -fipa-bit-cp.
If path is specified, GCC looks at the path to findthe profile feedback data files. See -fprofile-dir.
To optimize the program based on the collected profile information, use-fprofile-use. See Optimize Options, for more information.
-fprofile-note=pathIf path is specified, GCC saves .gcno file into pathlocation. If you combine the option with multiple source files,the .gcno file will be overwritten.
-fprofile-prefix-path=pathThis option can be used in combination withprofile-generate=profile_dir andprofile-use=profile_dir to inform GCC where is the basedirectory of built source tree. By default profile_dir will containfiles with mangled absolute paths of all object files in the built project.This is not desirable when directory used to build the instrumented binarydiffers from the directory used to build the binary optimized with profilefeedback because the profile data will not be found during the optimized build.In such setups -fprofile-prefix-path=path with pathpointing to the base directory of the build can be used to strip the irrelevantpart of the path and keep all file names relative to the main build directory.
-fprofile-update=methodAlter the update method for an application instrumented for profilefeedback based optimization. The method argument should be one of‘single’, ‘atomic’ or ‘prefer-atomic’.The first one is useful for single-threaded applications,while the second one prevents profile corruption by emitting thread-safe code.
Warning: When an application does not properly join all threads(or creates an detached thread), a profile file can be still corrupted.
Using ‘prefer-atomic’ would be transformed either to ‘atomic’,when supported by a target, or to ‘single’ otherwise. The GCC driverautomatically selects ‘prefer-atomic’ when -pthreadis present in the command line.
-fprofile-filter-files=regexInstrument only functions from files whose name matchesany of the regular expressions (separated by semi-colons).
For example, -fprofile-filter-files=main.c;module.*.c will instrumentonly main.c and all C files starting with ’module’.
-fprofile-exclude-files=regexInstrument only functions from files whose name does not matchany of the regular expressions (separated by semi-colons).
For example, -fprofile-exclude-files=/usr/.* will prevent instrumentationof all files that are located in the /usr/ folder.
-fprofile-reproducible=[multithreaded|parallel-runs|serial]Control level of reproducibility of profile gathered by-fprofile-generate. This makes it possible to rebuild programwith same outcome which is useful, for example, for distributionpackages.
With -fprofile-reproducible=serial the profile gathered by-fprofile-generate is reproducible provided the trained programbehaves the same at each invocation of the train run, it is notmulti-threaded and profile data streaming is always done in the sameorder. Note that profile streaming happens at the end of program run butalso before fork function is invoked.
Note that it is quite common that execution counts of some part ofprograms depends, for example, on length of temporary file names ormemory space randomization (that may affect hash-table collision rate).Such non-reproducible part of programs may be annotated byno_instrument_function function attribute. gcov-dump with-l can be used to dump gathered data and verify that they areindeed reproducible.
With -fprofile-reproducible=parallel-runs collected profilestays reproducible regardless the order of streaming of the data intogcda files. This setting makes it possible to run multiple instances ofinstrumented program in parallel (such as with make -j). Thisreduces quality of gathered data, in particular of indirect callprofiling.
-fsanitize=addressEnable AddressSanitizer, a fast memory error detector.Memory access instructions are instrumented to detectout-of-bounds and use-after-free bugs.The option enables -fsanitize-address-use-after-scope.See https://github.com/google/sanitizers/wiki/AddressSanitizer formore details. The run-time behavior can be influenced using theASAN_OPTIONS environment variable. When set to help=1,the available options are shown at startup of the instrumented program. Seehttps://github.com/google/sanitizers/wiki/AddressSanitizerFlags#run-time-flagsfor a list of supported options.The option cannot be combined with -fsanitize=thread.
-fsanitize=kernel-addressEnable AddressSanitizer for Linux kernel.See https://github.com/google/kasan/wiki for more details.
-fsanitize=pointer-compareInstrument comparison operation (<, <=, >, >=) with pointer operands.The option must be combined with either -fsanitize=kernel-address or-fsanitize=addressThe option cannot be combined with -fsanitize=thread.Note: By default the check is disabled at run time. To enable it,add detect_invalid_pointer_pairs=2 to the environment variableASAN_OPTIONS. Using detect_invalid_pointer_pairs=1 detectsinvalid operation only when both pointers are non-null.
-fsanitize=pointer-subtractInstrument subtraction with pointer operands.The option must be combined with either -fsanitize=kernel-address or-fsanitize=addressThe option cannot be combined with -fsanitize=thread.Note: By default the check is disabled at run time. To enable it,add detect_invalid_pointer_pairs=2 to the environment variableASAN_OPTIONS. Using detect_invalid_pointer_pairs=1 detectsinvalid operation only when both pointers are non-null.
-fsanitize=threadEnable ThreadSanitizer, a fast data race detector.Memory access instructions are instrumented to detectdata race bugs. See https://github.com/google/sanitizers/wiki#threadsanitizer for moredetails. The run-time behavior can be influenced using the TSAN_OPTIONSenvironment variable; seehttps://github.com/google/sanitizers/wiki/ThreadSanitizerFlags for a list ofsupported options.The option cannot be combined with -fsanitize=address,-fsanitize=leak.
Note that sanitized atomic builtins cannot throw exceptions whenoperating on invalid memory addresses with non-call exceptions(-fnon-call-exceptions).
-fsanitize=leakEnable LeakSanitizer, a memory leak detector.This option only matters for linking of executables andthe executable is linked against a library that overrides mallocand other allocator functions. Seehttps://github.com/google/sanitizers/wiki/AddressSanitizerLeakSanitizer for moredetails. The run-time behavior can be influenced using theLSAN_OPTIONS environment variable.The option cannot be combined with -fsanitize=thread.
-fsanitize=undefinedEnable UndefinedBehaviorSanitizer, a fast undefined behavior detector.Various computations are instrumented to detect undefined behaviorat runtime. Current suboptions are:
-fsanitize=shiftThis option enables checking that the result of a shift operation isnot undefined. Note that what exactly is considered undefined differsslightly between C and C++, as well as between ISO C90 and C99, etc.This option has two suboptions, -fsanitize=shift-base and-fsanitize=shift-exponent.
-fsanitize=shift-exponentThis option enables checking that the second argument of a shift operationis not negative and is smaller than the precision of the promoted firstargument.
-fsanitize=shift-baseIf the second argument of a shift operation is within range, check that theresult of a shift operation is not undefined. Note that what exactly isconsidered undefined differs slightly between C and C++, as well as betweenISO C90 and C99, etc.
-fsanitize=integer-divide-by-zeroDetect integer division by zero as well as INT_MIN / -1 division.
-fsanitize=unreachableWith this option, the compiler turns the __builtin_unreachablecall into a diagnostics message call instead. When reaching the__builtin_unreachable call, the behavior is undefined.
-fsanitize=vla-boundThis option instructs the compiler to check that the size of a variablelength array is positive.
-fsanitize=nullThis option enables pointer checking. Particularly, the applicationbuilt with this option turned on will issue an error message when ittries to dereference a NULL pointer, or if a reference (possibly anrvalue reference) is bound to a NULL pointer, or if a method is invokedon an object pointed by a NULL pointer.
-fsanitize=returnThis option enables return statement checking. Programsbuilt with this option turned on will issue an error messagewhen the end of a non-void function is reached without actuallyreturning a value. This option works in C++ only.
-fsanitize=signed-integer-overflowThis option enables signed integer overflow checking. We check thatthe result of +, *, and both unary and binary -does not overflow in the signed arithmetics. Note, integer promotionrules must be taken into account. That is, the following is not anoverflow:
-fsanitize=boundsThis option enables instrumentation of array bounds. Various out of boundsaccesses are detected. Flexible array members, flexible array member-likearrays, and initializers of variables with static storage are not instrumented.
-fsanitize=bounds-strictThis option enables strict instrumentation of array bounds. Most out of boundsaccesses are detected, including flexible array members and flexible arraymember-like arrays. Initializers of variables with static storage are notinstrumented.
-fsanitize=alignmentThis option enables checking of alignment of pointers when they aredereferenced, or when a reference is bound to insufficiently aligned target,or when a method or constructor is invoked on insufficiently aligned object.
-fsanitize=object-sizeThis option enables instrumentation of memory references using the__builtin_object_size function. Various out of bounds pointeraccesses are detected.
-fsanitize=float-divide-by-zeroDetect floating-point division by zero. Unlike other similar options,-fsanitize=float-divide-by-zero is not enabled by-fsanitize=undefined, since floating-point division by zero canbe a legitimate way of obtaining infinities and NaNs.
-fsanitize=float-cast-overflowThis option enables floating-point type to integer conversion checking.We check that the result of the conversion does not overflow.Unlike other similar options, -fsanitize=float-cast-overflow isnot enabled by -fsanitize=undefined.This option does not work well with FE_INVALID exceptions enabled.
-fsanitize=nonnull-attributeThis option enables instrumentation of calls, checking whether null valuesare not passed to arguments marked as requiring a non-null value by thenonnull function attribute.
-fsanitize=returns-nonnull-attributeThis option enables instrumentation of return statements in functionsmarked with returns_nonnull function attribute, to detect returningof null values from such functions.
-fsanitize=boolThis option enables instrumentation of loads from bool. If a value otherthan 0/1 is loaded, a run-time error is issued.
-fsanitize=enumThis option enables instrumentation of loads from an enum type. Ifa value outside the range of values for the enum type is loaded,a run-time error is issued.
-fsanitize=vptrThis option enables instrumentation of C++ member function calls, memberaccesses and some conversions between pointers to base and derived classes,to verify the referenced object has the correct dynamic type.
-fsanitize=pointer-overflowThis option enables instrumentation of pointer arithmetics. If the pointerarithmetics overflows, a run-time error is issued.
-fsanitize=builtinThis option enables instrumentation of arguments to selected builtinfunctions. If an invalid value is passed to such arguments, a run-timeerror is issued. E.g. passing 0 as the argument to __builtin_ctzor __builtin_clz invokes undefined behavior and is diagnosedby this option.
While -ftrapv causes traps for signed overflows to be emitted,-fsanitize=undefined gives a diagnostic message.This currently works only for the C family of languages.
-fno-sanitize=allThis option disables all previously enabled sanitizers.-fsanitize=all is not allowed, as some sanitizers cannot be usedtogether.
-fasan-shadow-offset=numberThis option forces GCC to use custom shadow offset in AddressSanitizer checks.It is useful for experimenting with different shadow memory layouts inKernel AddressSanitizer.
-fsanitize-sections=s1,s2,...Sanitize global variables in selected user-defined sections. si maycontain wildcards.
-fsanitize-recover[=opts]-fsanitize-recover= controls error recovery mode for sanitizersmentioned in comma-separated list of opts. Enabling this optionfor a sanitizer component causes it to attempt to continuerunning the program as if no error happened. This means multipleruntime errors can be reported in a single program run, and the exitcode of the program may indicate success even when errorshave been reported. The -fno-sanitize-recover= optioncan be used to alterthis behavior: only the first detected error is reportedand program then exits with a non-zero exit code.
Currently this feature only works for -fsanitize=undefined (and its suboptionsexcept for -fsanitize=unreachable and -fsanitize=return),-fsanitize=float-cast-overflow, -fsanitize=float-divide-by-zero,-fsanitize=bounds-strict,-fsanitize=kernel-address and -fsanitize=address.For these sanitizers error recovery is turned on by default,except -fsanitize=address, for which this feature is experimental.-fsanitize-recover=all and -fno-sanitize-recover=all is alsoaccepted, the former enables recovery for all sanitizers that support it,the latter disables recovery for all sanitizers that support it.
Even if a recovery mode is turned on the compiler side, it needs to be alsoenabled on the runtime library side, otherwise the failures are still fatal.The runtime library defaults to halt_on_error=0 forThreadSanitizer and UndefinedBehaviorSanitizer, while default value forAddressSanitizer is halt_on_error=1. This can be overridden throughsetting the halt_on_error flag in the corresponding environment variable.
Syntax without an explicit opts parameter is deprecated. It isequivalent to specifying an opts list of:
-fsanitize-address-use-after-scopeEnable sanitization of local variables to detect use-after-scope bugs.The option sets -fstack-reuse to ‘none’.
-fsanitize-undefined-trap-on-errorThe -fsanitize-undefined-trap-on-error option instructs the compiler toreport undefined behavior using __builtin_trap rather thana libubsan library routine. The advantage of this is that thelibubsan library is not needed and is not linked in, so thisis usable even in freestanding environments.
-fsanitize-coverage=trace-pcEnable coverage-guided fuzzing code instrumentation.Inserts a call to __sanitizer_cov_trace_pc into every basic block.
-fsanitize-coverage=trace-cmpEnable dataflow guided fuzzing code instrumentation.Inserts a call to __sanitizer_cov_trace_cmp1,__sanitizer_cov_trace_cmp2, __sanitizer_cov_trace_cmp4 or__sanitizer_cov_trace_cmp8 for integral comparison with both operandsvariable or __sanitizer_cov_trace_const_cmp1,__sanitizer_cov_trace_const_cmp2,__sanitizer_cov_trace_const_cmp4 or__sanitizer_cov_trace_const_cmp8 for integral comparison with oneoperand constant, __sanitizer_cov_trace_cmpf or__sanitizer_cov_trace_cmpd for float or double comparisons and__sanitizer_cov_trace_switch for switch statements.
-fcf-protection=[full|branch|return|none|check]Enable code instrumentation of control-flow transfers to increaseprogram security by checking that target addresses of control-flowtransfer instructions (such as indirect function call, function return,indirect jump) are valid. This prevents diverting the flow of controlto an unexpected target. This is intended to protect against suchthreats as Return-oriented Programming (ROP), and similarlycall/jmp-oriented programming (COP/JOP).
The value branch tells the compiler to implement checking ofvalidity of control-flow transfer at the point of indirect branchinstructions, i.e. call/jmp instructions. The value returnimplements checking of validity at the point of returning from afunction. The value full is an alias for specifying bothbranch and return. The value none turns offinstrumentation.
The value check is used for the final link with link-timeoptimization (LTO). An error is issued if LTO object files arecompiled with different -fcf-protection values. Thevalue check is ignored at the compile time.
The macro __CET__ is defined when -fcf-protection isused. The first bit of __CET__ is set to 1 for the valuebranch and the second bit of __CET__ is set to 1 forthe return.
You can also use the nocf_check attribute to identifywhich functions and calls should be skipped from instrumentation(see Function Attributes).
Currently the x86 GNU/Linux target provides an implementation basedon Intel Control-flow Enforcement Technology (CET).
-fstack-protectorEmit extra code to check for buffer overflows, such as stack smashingattacks. This is done by adding a guard variable to functions withvulnerable objects. This includes functions that call alloca, andfunctions with buffers larger than or equal to 8 bytes. The guards areinitialized when a function is entered and then checked when the functionexits. If a guard check fails, an error message is printed and the programexits. Only variables that are actually allocated on the stack areconsidered, optimized away variables or variables allocated in registersdon’t count.
-fstack-protector-allLike -fstack-protector except that all functions are protected.
-fstack-protector-strongLike -fstack-protector but includes additional functions tobe protected — those that have local array definitions, or havereferences to local frame addresses. Only variables that are actuallyallocated on the stack are considered, optimized away variables or variablesallocated in registers don’t count.
-fstack-protector-explicitLike -fstack-protector but only protects those functions whichhave the stack_protect attribute.
-fstack-checkGenerate code to verify that you do not go beyond the boundary of thestack. You should specify this flag if you are running in anenvironment with multiple threads, but you only rarely need to specify it ina single-threaded environment since stack overflow is automaticallydetected on nearly all systems if there is only one stack.
Note that this switch does not actually cause checking to be done; theoperating system or the language runtime must do that. The switch causesgeneration of code to ensure that they see the stack being extended.
You can additionally specify a string parameter: ‘no’ means nochecking, ‘generic’ means force the use of old-style checking,‘specific’ means use the best checking method and is equivalentto bare -fstack-check.
Old-style checking is a generic mechanism that requires no specifictarget support in the compiler but comes with the following drawbacks:
- Modified allocation strategy for large objects: they are alwaysallocated dynamically if their size exceeds a fixed threshold. Note thismay change the semantics of some code.
- Fixed limit on the size of the static frame of functions: when it istopped by a particular function, stack checking is not reliable anda warning is issued by the compiler.
- Inefficiency: because of both the modified allocation strategy and thegeneric implementation, code performance is hampered.
Note that old-style stack checking is also the fallback method for‘specific’ if no target support has been added in the compiler.
‘-fstack-check=’ is designed for Ada’s needs to detect infinite recursionand stack overflows. ‘specific’ is an excellent choice when compilingAda code. It is not generally sufficient to protect against stack-clashattacks. To protect against those you want ‘-fstack-clash-protection’.

-fstack-clash-protectionGenerate code to prevent stack clash style attacks. When this option isenabled, the compiler will only allocate one page of stack space at a timeand each page is accessed immediately after allocation. Thus, it preventsallocations from jumping over any stack guard page provided by theoperating system.
Most targets do not fully support stack clash protection. However, onthose targets -fstack-clash-protection will protect dynamic stackallocations. -fstack-clash-protection may also provide limitedprotection for static stack allocations if the target supports-fstack-check=specific.
-fstack-limit-register=reg-fstack-limit-symbol=sym-fno-stack-limitGenerate code to ensure that the stack does not grow beyond a certain value,either the value of a register or the address of a symbol. If a largerstack is required, a signal is raised at run time. For most targets,the signal is raised before the stack overruns the boundary, soit is possible to catch the signal without taking special precautions.
For instance, if the stack starts at absolute address ‘0x80000000’and grows downwards, you can use the flags-fstack-limit-symbol=__stack_limit and-Wl,--defsym,__stack_limit=0x7ffe0000 to enforce a stack limitof 128KB. Note that this may only work with the GNU linker.
You can locally override stack limit checking by using theno_stack_limit function attribute (see Function Attributes).
-fsplit-stackGenerate code to automatically split the stack before it overflows.The resulting program has a discontiguous stack which can onlyoverflow if the program is unable to allocate any more memory. Thisis most useful when running threaded programs, as it is no longernecessary to calculate a good stack size to use for each thread. Thisis currently only implemented for the x86 targets runningGNU/Linux.
When code compiled with -fsplit-stack calls code compiledwithout -fsplit-stack, there may not be much stack spaceavailable for the latter code to run. If compiling all code,including library code, with -fsplit-stack is not an option,then the linker can fix up these calls so that the code compiledwithout -fsplit-stack always has a large stack. Support forthis is implemented in the gold linker in GNU binutils release 2.21and later.
-fvtable-verify=[std|preinit|none]This option is only available when compiling C++ code.It turns on (or off, if using -fvtable-verify=none) the securityfeature that verifies at run time, for every virtual call, thatthe vtable pointer through which the call is made is valid for the type ofthe object, and has not been corrupted or overwritten. If an invalid vtablepointer is detected at run time, an error is reported and execution of theprogram is immediately halted.
How To Download Gcc On Mac Stack Overflow Download
This option causes run-time data structures to be built at program startup,which are used for verifying the vtable pointers. The options ‘std’ and ‘preinit’control the timing of when these data structures are built. In both cases thedata structures are built before execution reaches main. Using-fvtable-verify=std causes the data structures to be built aftershared libraries have been loaded and initialized.-fvtable-verify=preinit causes them to be built before sharedlibraries have been loaded and initialized.
If this option appears multiple times in the command line with differentvalues specified, ‘none’ takes highest priority over both ‘std’ and‘preinit’; ‘preinit’ takes priority over ‘std’.
-fvtv-debugWhen used in conjunction with -fvtable-verify=std or -fvtable-verify=preinit, causes debug versions of the runtime functions for the vtable verification feature to be called. This flag also causes the compiler to log information about which vtable pointers it finds for each class.This information is written to a file named vtv_set_ptr_data.log in the directory named by the environment variable VTV_LOGS_DIR if that is defined or the current working directory otherwise.
Note: This feature appends data to the log file. If you want a fresh logfile, be sure to delete any existing one.
-fvtv-countsThis is a debugging flag. When used in conjunction with-fvtable-verify=std or -fvtable-verify=preinit, thiscauses the compiler to keep track of the total number of virtual callsit encounters and the number of verifications it inserts. It alsocounts the number of calls to certain run-time library functionsthat it inserts and logs this information for each compilation unit.The compiler writes this information to a file namedvtv_count_data.log in the directory named by the environmentvariable VTV_LOGS_DIR if that is defined or the current workingdirectory otherwise. It also counts the size of the vtable pointer setsfor each class, and writes this information to vtv_class_set_sizes.login the same directory.
Note: This feature appends data to the log files. To get fresh logfiles, be sure to delete any existing ones.
How To Download Gcc On Mac
-finstrument-functionsGenerate instrumentation calls for entry and exit to functions. Justafter function entry and just before function exit, the followingprofiling functions are called with the address of the currentfunction and its call site. (On some platforms,__builtin_return_address does not work beyond the currentfunction, so the call site information may not be available to theprofiling functions otherwise.)
The first argument is the address of the start of the current function,which may be looked up exactly in the symbol table.
This instrumentation is also done for functions expanded inline in otherfunctions. The profiling calls indicate where, conceptually, theinline function is entered and exited. This means that addressableversions of such functions must be available. If all your uses of afunction are expanded inline, this may mean an additional expansion ofcode size. If you use extern inline in your C code, anaddressable version of such functions must be provided. (This isnormally the case anyway, but if you get lucky and the optimizer alwaysexpands the functions inline, you might have gotten away withoutproviding static copies.)
A function may be given the attribute no_instrument_function, inwhich case this instrumentation is not done. This can be used, forexample, for the profiling functions listed above, high-priorityinterrupt routines, and any functions from which the profiling functionscannot safely be called (perhaps signal handlers, if the profilingroutines generate output or allocate memory).See Common Function Attributes.
-finstrument-functions-exclude-file-list=file,file,…Set the list of functions that are excluded from instrumentation (seethe description of -finstrument-functions). If the file thatcontains a function definition matches with one of file, thenthat function is not instrumented. The match is done on substrings:if the file parameter is a substring of the file name, it isconsidered to be a match.
For example:
excludes any inline function defined in files whose pathnamescontain /bits/stl or include/sys.
If, for some reason, you want to include letter ‘,’ in one ofsym, write ‘,’. For example,-finstrument-functions-exclude-file-list=',tmp'(note the single quote surrounding the option).

-finstrument-functions-exclude-function-list=sym,sym,…This is similar to -finstrument-functions-exclude-file-list,but this option sets the list of function names to be excluded frominstrumentation. The function name to be matched is its user-visiblename, such as vector<int> blah(const vector<int> &), not theinternal mangled name (e.g., _Z4blahRSt6vectorIiSaIiEE). Thematch is done on substrings: if the sym parameter is a substringof the function name, it is considered to be a match. For C99 and C++extended identifiers, the function name must be given in UTF-8, notusing universal character names.
-fpatchable-function-entry=N[,M]Generate N NOPs right at the beginningof each function, with the function entry point before the Mth NOP.If M is omitted, it defaults to 0 so thefunction entry points to the address just at the first NOP.The NOP instructions reserve extra space which can be used to patch inany desired instrumentation at run time, provided that the code segmentis writable. The amount of space is controllable indirectly viathe number of NOPs; the NOP instruction used corresponds to the instructionemitted by the internal GCC back-end interface gen_nop. This behavioris target-specific and may also depend on the architecture variant and/orother compilation options.
For run-time identification, the starting addresses of these areas,which correspond to their respective function entries minus M,are additionally collected in the __patchable_function_entriessection of the resulting binary.
Note that the value of __attribute__ ((patchable_function_entry(N,M))) takes precedence over command-line option-fpatchable-function-entry=N,M. This can be used to increasethe area size or to remove it completely on a single function.If N=0, no pad location is recorded.
The NOP instructions are inserted at—and maybe before, depending onM—the function entry address, even before the prologue.
How To Download Gcc On Mac Stack Overflow Chrome
The maximum value of N and M is 65535.
How To Download Gcc On Mac Stack Overflow Tank
Next: Preprocessor Options, Previous: Optimize Options, Up: Invoking GCC [Contents][Index]